Fri, Mar 8, 2024
Including Digital Risk Protection in Your Threat Detection and Response Strategy
Many organizations focus on addressing the risks within their internal attack surface while overlooking the potential threats created by their external digital footprint on the surface, deep and dark web. This article outlines how companies can significantly mitigate this risk by combining digital risk protection with their detection and response approach.
An effective detection and response capability is essential for monitoring key assets and ensuring that they are comprehensively defended. Traditional detection and response strategies focus on detecting threats as early as possible during an attack, with the aim of containing and eradicating them before they can cause damage. Despite continuous investment in their internal defenses, businesses continue to fall victim to persistent cyberattacks. This is because they overlook their external defenses in addressing the risks associated with all levels of the internet.
Organizations have a greater chance of reducing the likelihood and impact of an attack if they can extend their detection efforts into their external digital footprint across the surface, deep and dark web. Companies intending to use or currently using managed threat detection and response (MDR) services can benefit by combining them with digital risk protection. By adding external sources into their threat detection and response strategy, they can extend visibility into the earliest stages of an attack, reconnaissance and resource development tactics as well as the post-compromise stages of an attack (such as extortion or the sale of IP, as shown in Figure 1).
Figure 1: Digital risk protection provides additional coverage of adversary tactics before and after a compromise.
What is Digital Risk Protection?
Digital risk protection is a branch of threat intelligence that provides pre- and post-compromise visibility by continuously monitoring the surface, deep and dark web for potential signs of targeted attacks or existing data leakage on parts of the web that are hidden from search engines, unindexed or obfuscated in closed communities.
Pre-compromise, being armed with this type of intelligence can help security teams enhance their defenses on the basis of greater clarity on exactly who is planning to attack the organization and how they plan to do it.
Post-compromise, this insight can provide security teams with early signs of a breach and enable them to take necessary action to limit its potential impact.
Digital Risk Protection also helps to protect brand reputation by scanning the surface web for brand misuse, impersonation and domain spoofing that could lead to threats against employees, customers and suppliers.
Why the Deep and Dark Web Should be Part of Your Threat Detection Strategy
With the deep and dark web making up approximately 96% of the internet that is unindexed, obscured or intentionally difficult to find, it’s no surprise that cybercriminals are constantly taking advantage of it to plan their attacks or sell stolen information onto persistent threat actors for further compromise. Dark web monitoring can play an important role in addressing the risk this creates for organizations.
What is Dark Web Monitoring?
Dark web monitoring provides a proactive, intelligence-driven approach for gauging exposure and defending against threats both before and after compromise. It works in three ways:
-
Pre-empting Targeted Attacks
A cyberattack doesn’t start on the network; it is planned in dark web forums and hacking sites, where threat actors conduct reconnaissance, sell company data to other threat actor groups and prepare resources to target their intended victim out of reach of cybersecurity teams and law enforcement.
Dark web intelligence provides security teams with the adversarial knowledge required to pre-empt and prevent attacks, reducing the reputational and financial impact of cybercrime on their business. -
Identifying a Past or Ongoing Breach
Discovering stolen customer lists or data, employee login credentials and email domains and IP addresses on the dark web can help your organization identify an ongoing data breach or a data breach that has occurred in the past. By identifying attacks (such as account takeovers or data leakage) at an earlier stage, businesses can mitigate the damage to their financial status and reputation. -
Mitigating Inherited Vulnerabilities or Exposures from Mergers/Acquisitions
As part of due diligence on a company that is a target for acquisition or merger, understanding the extent to which their sensitive data has been exposed can be critical information. The inadvertent exposure of that sensitive information can have a significant negative impact on the party or parties involved. This could include reputational damage, a decrease in the value of assets and even becoming the target for further cyberattacks.
Gaining this information after the merger or acquisition has been completed can also help to ensure that vulnerabilities or exposures are not inherited and that defenses are updated if an exposure or data leakage has occurred.
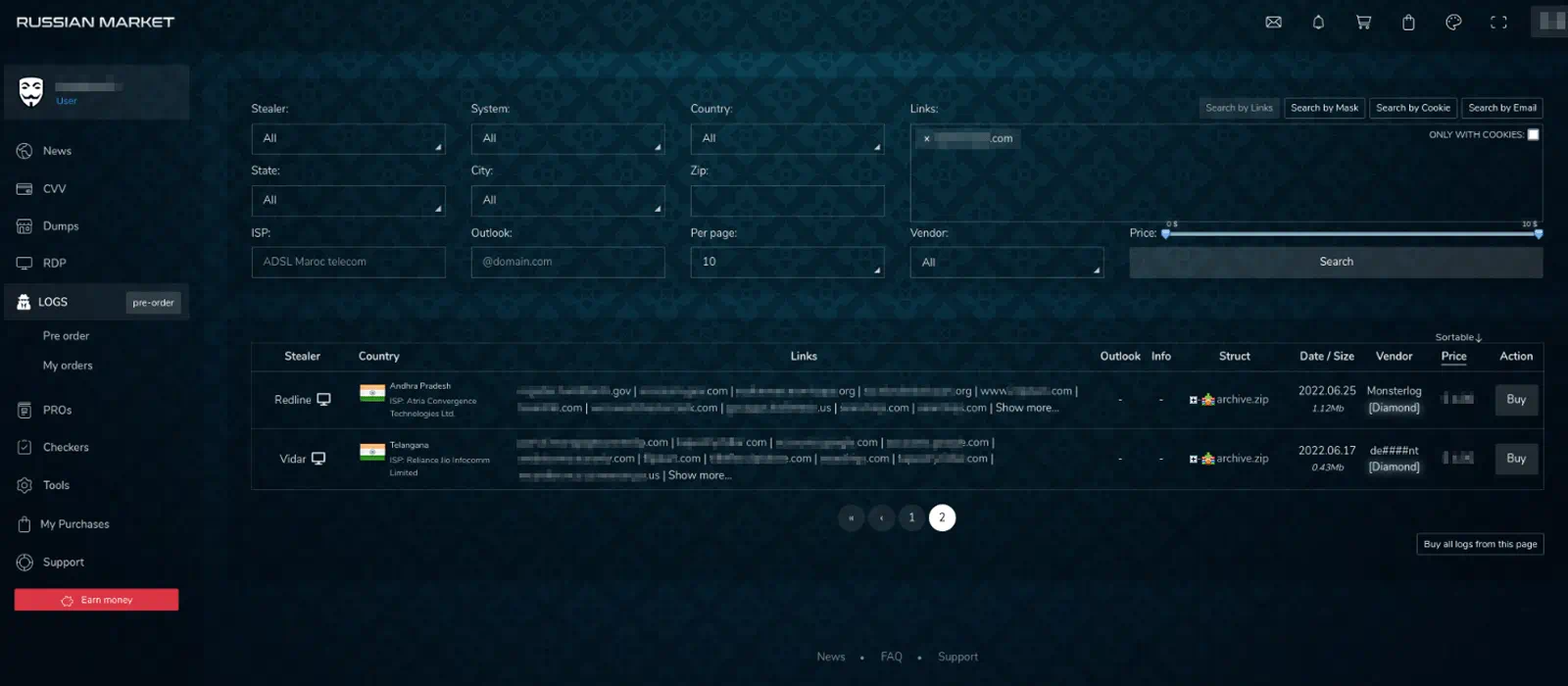
Figure 2: Russian Market is a marketplace where actors can buy listings which contain saved data from browser extensions (e.g. usernames, passwords, cookies). Once the actor buys the listing, they can then try to access those domains/resources using the saved information
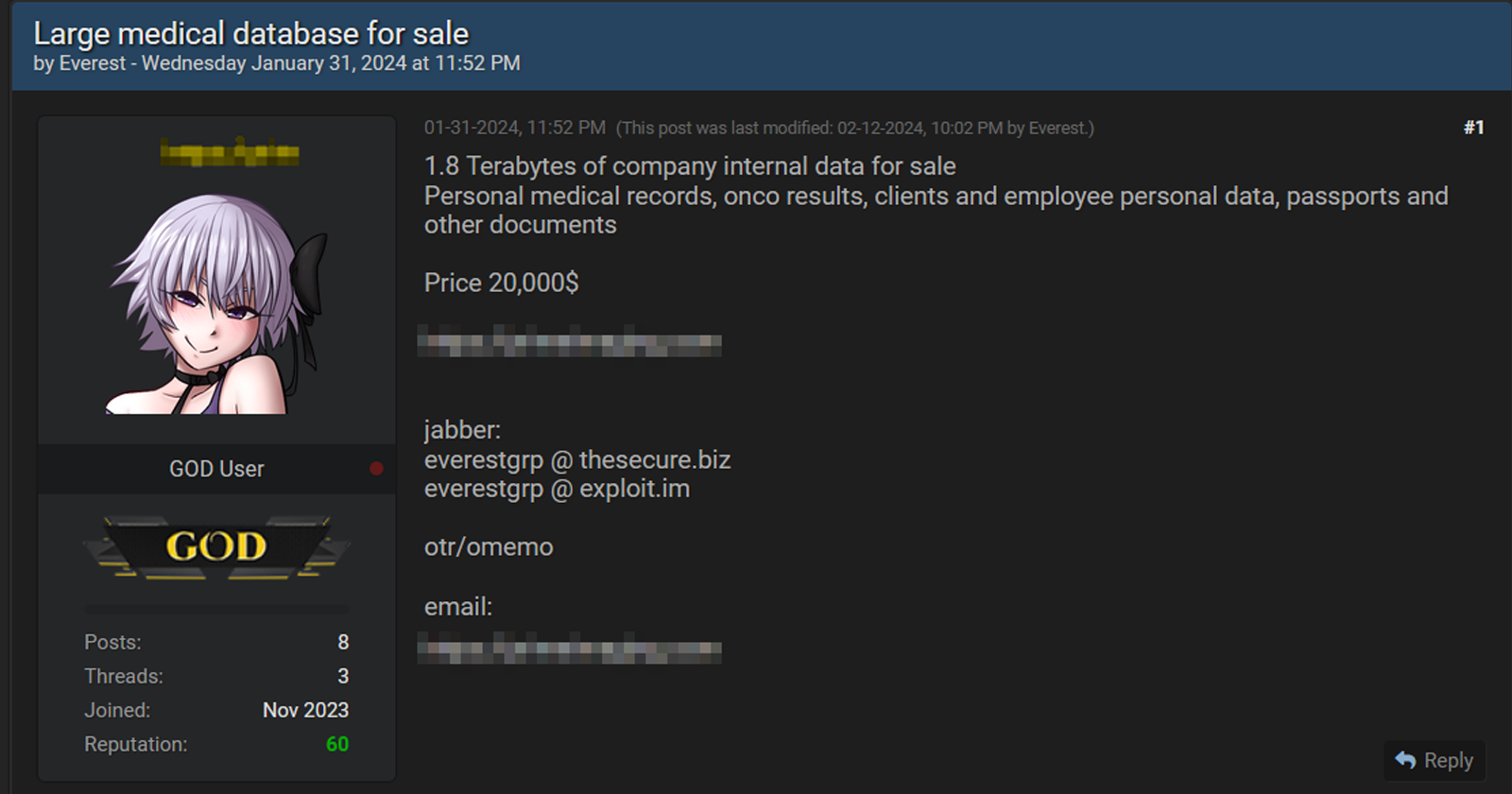
Figure 3: Medical database stolen from a health care provider being sold by a threat actor to the underground community
Why Use Surface Web Monitoring for Brand Protection?
Alongside the serious risks presented by the deep and dark web, organizations should also carefully monitor for those associated with the surface web. Integrating surface web within your threat detection and response strategy is especially valuable for organizations’ that rely heavily on brand reputation. This includes medium to large enterprises where company brand is a significant risk, such as retail and e-commerce companies, banking and finance institutions and industries holding highly sensitive data for multiple stakeholders (e.g., private equity, law firms, insurance and health care).
Attackers may target these types of businesses to create fake websites in their name or impersonate their domains to launch phishing attacks on their customers. Brand/domain monitoring can help organizations mitigate these risks by keeping track of the open web for domain impersonations, threats to company executives, spoofed websites and social media profiles.
However, as important as it is, monitoring is only one side of effective brand and domain defense. It should be followed with swift response using threat takedowns. This is where evidence is gathered and submitted as part of a formal request to the source platform owner, such as the internet service provider or platform owner for them to remove harmful content from the internet. As a time-consuming and specialized process, this should be managed by takedown experts with proven expertise in how to format and submit valid takedown requests to law enforcement, domain registrars and hosting sites.
Common Surface Web Use Cases
Use Case | Attack Scenario | How Surface Web Monitoring Helps |
|---|---|---|
Domain Spoofing and Phishing | Attackers create domain names by manipulating your brand and targeting your customers, suppliers or internal employees to compromise their data. This is done by continuously creating look-a-like domains with a couple of characters that are different from those of the legitimate domain name. These spoofed domains are used to create phishing sites, sell counterfeit products or steal login credentials. Threat actors will then also use these domains to conduct business email compromise (BEC) scams, deliver malware and create ransomware attack lures. | Brand and domain monitoring services use a list of target domains and/or brand keywords to search across the surface web for signs of spoofed sites that use typosquatting or other copycat techniques and can initiate a takedown request with the internet service provider by providing evidence of the threat. |
Brand Misuse and Impersonation (Web/Social/Mobile Apps) | Cybercriminals create fake apps and social media profiles designed to impersonate your brand. They can then use these compromised channels to scam customers, spread misinformation to impact share prices and take over mobile devices using malware, or facilitate browser hijacking. | Surface web monitoring hunts for misinformation and brand impersonations across the web, social media and mobile app stores. Human analysts then work directly with the app stores or social media platforms to ensure that the fake content is removed. |
VIP/Executive Protection | Executives are targeted for a variety of online attacks due to their high visibility and high value. | Mitigates online abuse with content moderation on owned and paid social content to safeguard VIPs’ digital spaces. |
Addressing Gaps in the MITRE ATT&CK Matrix with Digital Risk Protection
The MITRE ATT&CK framework is commonly associated with tactics, techniques and procedures (TTPs) that can be put into network, endpoint or cloud detection controls. However, the framework is also useful for showing how dark web intelligence can shine a light on attackers right at the beginning of their campaigns, informing organizations’ defenses so that they can stop their adversaries at the first stage of the “kill chain.” This means that leveraging digital risk protection services give organizations a much better chance of identifying the tactics that could be at risk of being overlooked by MDR services.
Examples of this include:
-
Active Scanning (T1595)
Adversaries execute active reconnaissance scans to gather information that can be used during targeting, probing the victim’s infrastructure via network traffic. -
Compromise Accounts - Social Media Accounts (T1586.001)
Adversaries may compromise social media accounts that can be used during targeting. For operations incorporating social engineering, the utilization of an online persona may be important. -
Gather Victim Identity Information (T1589)
Adversaries gather information about the victim’s identity that can be used during targeting. This information may include personal data such as employee names and email addresses as well as sensitive details, such as credentials. -
Gather Victim Network Information (T1590)
Adversaries may gather information about the victim's networks that can be used during targeting. Information about networks may include a variety of details, including administrative data, such as IP ranges and domain names, as well as specifics regarding topology and operations. -
Compromise Infrastructure (T1584.001)
Adversaries may hijack domains and/or subdomains that can be used during targeting. Domain registration hijacking is the act of changing the registration of a domain name without the permission of the original registrant. Adversaries may gain access to an email account for the person listed as the owner of the domain. -
Search Closed Sources (T1597)
Adversaries search and gather information about victims from closed sources. This information can be used during targeting. It may be available for purchase from reputable private sources and databases, such as paid subscriptions to feeds of technical or threat intelligence data. -
Search Open Technical Domains (T1596)
Adversaries may search freely available technical databases for information about victims that can be used during targeting. This type of data may be available in online databases and repositories, such as registrations of domains and certificates as well as public collections of network data and artifacts gathered from traffic and/or scans. -
Acquire Access (T1650)
Adversaries may purchase or otherwise acquire an existing access to a target system or network. A variety of online services and initial access broker networks sell access to previously compromised systems. In some cases, adversary groups may form partnerships to share compromised systems with each other. -
Obtain Capabilities (T1588)
Adversaries may obtain capabilities to support their operations throughout numerous phases of the adversary lifecycle. Rather than developing their own capabilities in-house, they may purchase, freely download or steal them. Activities can include the acquisition of malware, software (including licenses), exploits, certificates and information relating to vulnerabilities.
Monitoring your Exposure on the Surface, Deep and Dark Web: Key Challenges
While digital risk protection across the surface, deep and dark web is a valuable data source for threat detection activities, organizations can face a number of challenges when integrating it into their detection and response strategy. These include:
-
Issues With In-House Implementation
Bringing dark web monitoring in-house can be costly and time-consuming. Depending on your specific needs and intended outcomes, it can demand specialized skills, such as fluency in non-English languages used by global threat actors, and time to access the forums, marketplaces and other arenas used by attackers to share data. -
Limited Context for Turning Feeds Into Action
Internal security teams often find it difficult to deduce which types of threats to prioritize, not only because of the number of threat intelligence feeds they subscribe to, but also due to the limited context provided by those feeds. For example, they may focus on the individual observables, such as domains and malicious IP addresses, but lack insight into the types of businesses being exploited by these threats or how best to mitigate them in the future. -
Intelligence Gathered Without Experience
If approached in the wrong way, attempting to access intel from cybercriminal sources can put your company or employees in danger of being targeted. Cybercriminals are highly vigilant about who they allow to access their closed forums and communities. One wrong move could mean clicking on sites or downloading files that infect your systems and put you in line for persistent future attacks. -
Lack of Human Validation
A high volume of threat intelligence is machine-generated and simply ingested straight into detection technologies or placed in a report without human validation. This is especially important when consuming multiple feeds, as they won’t all be relevant to your unique threat profile. However, without expert analysts to triage these feeds, remove the less relevant data and explore the highlighted forums, marketplaces or chat messages for further information, your security teams may become over-burdened by dealing with irrelevant noise and miss other potential security threats as a result.
MDR + Digital Risk Protection: Reducing Risk, Enhancing Value
Combining managed detection and response with digital risk protection delivers key security advantages to organizations, including:
- Benefits from alerting on both internal and external threat activity in one portal - Having both alerts from your internal controls and from the dark web in one interface allows you to maintain visibility of threats in the wild and in your network. It also provides more context at greater speed into threats in your environment, such as previously leaked or stolen information.
- Extend visibility of threat activity across the attack chain, from pre-, during and post-compromise - Supplementing your MDR service with dark web monitoring provides extended visibility across the entire attacker lifecycle, giving you additional layers of defense:
- The opportunity to stop a planned attack in its tracks before it hits your network
- If an attack does enter your network, you have visibility but can also respond to contain it; and
- If the attack is successful or if it has compromised a previously unmonitored endpoint, you can identify early on exactly which data has been leaked.
- Use surface, deep and dark web intel to supplement new detection use cases - This intelligence gives your security operations teams additional indicators of compromise (IoCs) to monitor, which in turn can be a new source for creating adversary-driven detection rules and playbooks. Being armed with this additional intelligence can refocus your security controls and proactively indicate new security policies and hardening priorities.
- Extend response beyond detection - Some providers, such as Kroll, also offer takedown services to enable organizations to act swiftly and effectively in response to any signs of brand impersonation, such as typo squatting or phishing campaigns. This goes beyond detection to extend response capability in order to take down external threats.
How Kroll Can Help
Detect threats before anyone else in your industry while maintaining end-to-end visibility and proactive response through Kroll’s digital risk protection expertise coupled with our Responder MDR service. Threat intelligence drawn from our status as the world’s leading incidence response (IR) provider and 3,000+ IR engagements a year fuels our MDR and threat intelligence services by providing tailored insight into adversary behavior and earlier detection of malicious activities.
We leverage industry-leading intelligence collection technology and human expertise to find exposed, stolen or leaked company information on the deep and dark web. Our analysts utilize proprietary information collected from investigations and closed sites used by criminals to gain early insights into activity that could indicate a targeted attack on your organization.
Discover Our Digital Risk Protection Services
Cyber Risk
Incident response, digital forensics, breach notification, managed detection services, penetration testing, cyber assessments and advisory.
Digital Risk Protection
Proactively safeguard your organization’s digital assets and accelerate visibility of online threats.
Cyber Threat Intelligence
Threat intelligence are fueled by frontline incident response intel and elite analysts to effectively hunt and respond to threats.
Kroll Responder MDR
Stop cyberattacks. Kroll Responder managed detection and response is fueled by seasoned IR experts and frontline threat intelligence to deliver unrivaled response.
Managed Security Services
World-renowned cyber investigators and leading technology fuel Kroll’s managed security services, augmenting security operations centres and incident response capabilities.
24x7 Incident Response
Kroll is the largest global IR provider with experienced responders who can handle the entire security incident lifecycle.





